The web is intended to help a person find and understand relevant information. The primary container of information is the document. Therefore web applications should be centered around a document metaphor, not an app one.
In 1990 Tim Berners-Lee and Robert Cailliau wrote a proposal for what we call the web today:
HyperText is a way to link and access information of various kinds as a web of nodes in which the user can browse at will.
The web is a linked information system. Bret Victor states:
Information software serves the human urge to learn. A person uses information software to construct and manipulate a model that is internal to the mind — a mental representation of information.
The web is built around information. More information than we can handle. What we need to make sense of it all is understanding. The power of technology can be used to transfer and gain understanding. Understanding needs to be a first class citizen. The applications we build must be centered around it.
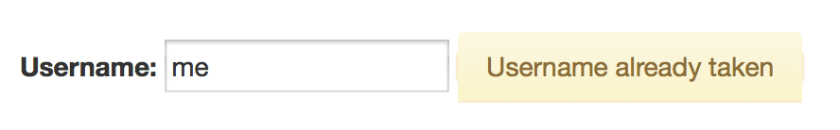
One way to foster understanding is to interact, to play with information. Technology can simulate a system of information so that we can form hypotheses and ask questions. Bret Victor coined the term “explorable explanations” to describe such systems.
I believe the web is perfectly suited for building explorable explanations.
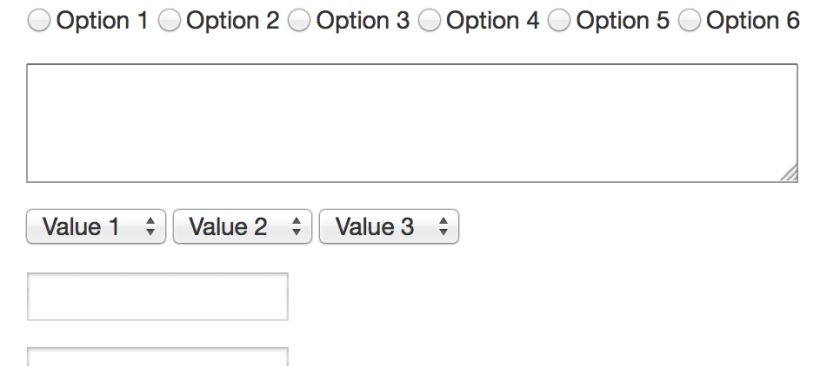
The web’s container for information is the document. A document combines different forms of media (text, images, video, …) to a whole. Fortunately for us the web does not stop here. With scripting we have the possibility to interact and manipulate the information in order to gain further insight.
Most of the tools we need to create for understanding are already at our hands. What we need is a fundamental change in focus. Right now (a large part of) the web industry tries to play catch up with native. Whole frameworks try to mimic native applications like this is a virtue. Current developments want to abstract the document as far away as possible. This is not what the web was intended for. Why build an application which tries so hard to recreate a native feeling in something other than the native platform itself? Web applications should be built on the strength of the web. We should not chase a foreign metaphor.
Right now the web seems to be torn. Torn between the print era of passive documents and the shiny new world of native applications. But the web has the capability to do so much more. To concentrate on its purpose, to fill the niche. A massive niche. Understanding is a core endeavor of mankind. To quote Stephen Anderson and Karl Fast in introducing their upcoming book From Information to Understanding:
In all areas of life, we are surrounded by understanding problems.
Doug Engelbart shares a similar vision for the purpose of the personal computer per se:
By “augmenting human intellect” we mean increasing the capability of a man to approach a complex problem situation, to gain comprehension to suit his particular needs, and to derive solutions to problems.
The web is ready. The tools are ready. But are we?
Where to start: foundations
- How to make sense of any mess Information architecture for everybody
- Explorable explanations A start for exploring explorable explanations
- The visual display of quantitative information and everything else by Edward Tufte (the bibles of information design)
- Mental notes Nuggets of insight into the human behavior and how to apply these to web design
- Understanding comics A book about how we deal with visual languages
- Psychology of information (in German) a compendium which brings together the different fields of psychology regarding information design