One might love Open Source for different reasons: Maybe as a philosophical concept of transcendental sharing and human progress, maybe for reasons of transparency and security, maybe for the sole reason of getting stuff for free…
But, as a developer, Open Source is additionally appealing for the sake of actively participating, learning and sharing on a directly personal level.
Now I would guess that most repository forks are probably done for rather practical reasons (“I wanna have that!”), the forks get some minor patches one happens to need right now – or for some super-specific use case – and then hang around for some time until that use case vanishes or the changes are so vast that there will never be a merge (a situation commonly known as “der Zug ist abgefahren”), one might sometimes try to supply one’s work for the good of more than oneself. That is what I hereby declare a “Fork in Good Faith.”
A fork can happen in good faith if some conditions are true, like:
- I am sure that someone else can benefit from my work
- My technical skills match the technical level of the repository in question
- Said upstream repository is even open for contributions (i.e. not understaffed)
- My broader vision does not diverge from the original maintainers’ vision
Maybe there are more of these, but the most essential point is a mindset:
- I declare to myself that I want to stay compatible with the upstream as long as is possible from both sides.
To fork with Good Faith is, then, a great idea because it helps to advance much more causes at once than just the stuff for free, i.e. on a developmental level:
- You learn from the existing code, i.e. the language, coding style, design patterns, specific solutions, algorithms, hidden gems, …
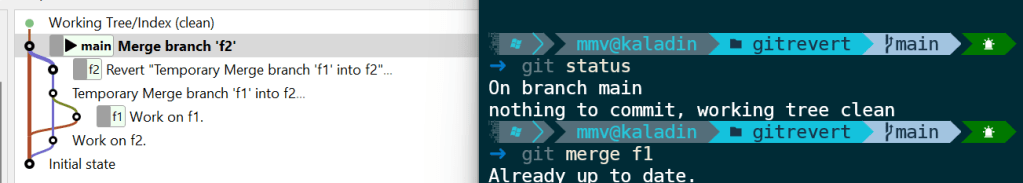
- You learn from the existing repository, i.e. how commits and branches are organized, how commit messages are used productively, how to manage patches or changes in general, …
- In reverse, the original maintainers might learn from you, or at least future contributors might
- You might get more people to actually see / try / use your awesome feature, thus getting more feedback or bug reports than brewing your own soup
- You might consider it as a workout of professional confidence, to advocate your use cases or implementation decisions against other developers, training to focus on rational principles and unlearning the reflexes of your ego.
- This can also serve as a workout in mental fluidity, by changing between different coding styles or conventions – if you are e.g. used of your super-perfect-one-and-only way of doing things, it might just positively blow your mind to see that other conventions can work too, if done properly.
- Having someone to actually review your changes in a public pull request (merge request) gives you feedback also on an organisational level, as in “was all of this part actually important for your feature?”, “can you put that into a future pull request?” or “why did you rewrite all comments for some Paleo-Siberian language??”
Not to forget, you might grow your personal or professional network to some degree, or at least get the occasional thank you from anyone (well…).
But the basic point of this post is this:
Maintaining a Fork in Good Faith is active, continuous work.
And there is no shame in abandoning that claim, but if you do once, there might be no easy return.
Just think about the pure sadness of features that are sometimes replicated over-and-over again, or get lost over the time;
And just think about how confusing or annoying that already could have been for yourself, e.g. with some multiply-forked npm package or maybe full-fledged end-user projects (… how many forks of e.g. WLED do even exist?).
This is just some reflection of how careful such a decision should be done. Of course, I am writing this because I recently became aware of that point of bifurcation, i.e. not the point where a repository is forked, but the one where all of the advantages mentioned above are weighed against real downsides.
And these might be legitimate, and numerous, too. Just to name a few,
- Maybe the existing conventions are just not “done properly”, and following them for the sake of uniformity makes you unproductive over time?
- Maybe the original maintainers are just understaffed, non-responsive or do not adhere to a style of communication that works with you?
- Maybe most discussions are really just debates of varying opinion (publicly, over the internet – that usually works!) and not vehicles of transcending the personal boundaries of human knowledge after all?
- Maybe you are stuck with sub-par legacy code, unable to boy-scout away some technical debt because “that is not the point right now”, or maybe every other day some upstream commit flushes in more freshly baked legacy code?
- Maybe no one understands your use case and contrary to the idea mentioned above – in order to get appropriate feedback about your features, and to prove its worth, you need to distribute this independently?
- Maybe at one point the maintainers of an upstream repository change, and from now on you have to name your variables in some Paleo-Siberian language?
I guess you get the point by now. There is much energy to be saved by never considering upstream compatibility in the first place, but there is also much potential to be wasted. I have no clear answer – yet – how to draw the line, but maybe you have some insight on that topic, too.
Are there any examples of forks that live on their own, still with the occasional cherry-pick, rebase, merge? Not one comes to my mind.